PC load letter? What the fuck does that mean?
- 1 Post
- 109 Comments

 6·15 天前
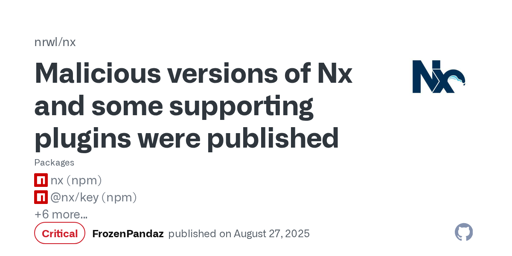
6·15 天前The command injection in the GitHub action code was written by Claude[1]. That was used to get the NPM key and then malware was pushed to NPM.

 3·2 个月前
3·2 个月前Yes social engineering can be incredibly effective. I completely agree, but there is a bit of an obsession with it these days and imo it’s over indexed, because at the end of the day the type of social engineering detailed in that report typically just provides access.
In some cases, the target is important enough and has enough organizational power that accessing the network as them is sufficient, but that’s not often the case. What that means is that in those other cases social engineering (which in that report you cited is often just phishing) is providing, typically, internal network access. An attacker will have to move through the network and exploit software typically to continue their attack. There are many points in this chain that the weakness lies in software or configuration. If effort was placed on making those systems better it would likely see better results than hyper focusing on the social engineering, which is significantly more difficult to stop, especially with all of the things you mentioned on the horizon.
My point is then that even if it is a part of 74% of breaches, according to Verizon, it’s not necessarily sufficient and is often paired with software level exploits.
And I know this because my company does plenty of red teaming, and we use social engineering but at the end of the day the more interesting result comes from a software exploit or just abusing a weak configuration.

 3·2 个月前
3·2 个月前I have found the exact same type of bug shown here probably over a dozen times, most of those long before AI was writing code.

 4·2 个月前
4·2 个月前Not a big fan of the wording here. Plenty of skilled programmers make dumb mistakes. There should always be systems in place to ensure these dumb mistakes don’t make it to production. Especially when related to sensitive information. Where was the threat model and the system in place to enforce it? The idea that these problems are caused by “shit programmers” misses the real issue: there was either no system or an insufficient system to test features and define security requirements.

 23·2 个月前
23·2 个月前I work in security and I kinda doubt this. There are plenty of issues just like what is outlined here that would be much easier to exploit than social engineering. Social engineering costs a lot more than
GET /secrets.json.There is good reason to be concerned about both, but 95% sounds way off and makes it sound like companies should allocate significantly more time to defend against social engineering, when they should first try to ensure social engineering is the easiest way to exploit their system. I can tell you from about a decade of experience that it typically isn’t.
I don’t think they meant everything literally goes in the same direction, but more like what is discussed here https://www.scientificamerican.com/article/do-we-live-inside-a-black-hole/ (this article was shared elsewhere in this post)
Not really, but I’d probably try to organize those into sub structures where it made sense. A data structure holding the UI state and FFT data all flat is kinda messy imo since it becomes unclear what is actually required where.
QEMU makes it pretty painless to hook up gdb just FYI; you should look into that. I think you can also have it provide a memory mapped UART for I/O which you can use with newlib to get printf debugging

 10·4 个月前
10·4 个月前Pretty much everyone I work with uses vim, emacs, sublime, or vscode. I like IDEs and use them for… well Java, but I wouldn’t argue that they’ve made the other tools obsolete or you’re a fool for sticking with the old ones. If it ain’t broke and all that. It actually seems like more people are moving back to pluggable text editors over IDEs
I’ve used AI tools a bit. They’ve really helped drop in code that would previously just be a bunch of TODOs; they get you up and writing the core parts much faster to see if the idea even works. They’ve also really helped answer specific questions or lead me towards the answer. They’ve also straight up lied to me quite a bit. It’s a weird tool.
I think the OP image is pretty wrong with the comparison it makes. LLMs/AI are a class of technology that are most definitely not going anywhere unless something dramatic happens. Some people, myself included, feel uneasy about the way they’re created and the fact that people in powerful positions completely misunderstand them, and I think that leads to the hope that they’re just a fad.
Could be a variable from somewhere else in the code. It should throw type error of some sort if it’s not going to handle a float correctly
I travel a bunch and have lived abroad and I always consistently only ever miss breakfast restaurants/diners and breakfast foods.

 1·5 个月前
1·5 个月前TIL I didn’t realize Java used UTF16 for its internal representation. Looks like it’s a bit more complicated than that after Java 9 too

 6·5 个月前
6·5 个月前Android defaults to UTF16
It is a fantastic way to make sure things work across a team. We use Linux (bunch of different distro) and macOS at my company and once I started packaging things with nix environment related issues mostly went away. It’s not perfect and it’s not necessarily easy to learn nix, but I prefer it to sharing docker containers or other alternatives.
In some build modes clang will simply put a trap where it sees undefined behavior. https://clang.llvm.org/docs/UndefinedBehaviorSanitizer.html
Not saying your wrong, just a fun fact I guess
Sorry I didn’t mean to imply they don’t use shared libs, they definitely do, but they have to integrate them into the larger system still and put consistent interfaces over them.



Not exactly “memory address 0”; there be dragons there. https://c-faq.com/null/index.html